RFID According to Frequency Range - Do You Know What You Are Dealing With?
RFID technology is a common part of our daily lives. Where do we come into contact with it and what are the most common risks? This article lists selected attack vectors and outlines real everyday situations in which we can encounter fraud in the RFID environment. The main goal of this article is an introductory and brief division of RFID technology according to the frequency band in which the actual communication takes place, including the primary areas of use.
Most of us have already heard about the RFID technology. Some of us may be using and not even realize it. It has become a regular part of our lives. We can find it as a security element on goods in the store, or maybe we have an access card or chip to a secured object. We also use it when travelling by public transport or for payments at merchants.
And what about security? The vast majority of people are probably not much concerned about it. For example, convinced opponents of contactless payments will avoid them like the plague, others will be fine with a certain amount of caution, defined limits, and in the best case, they will have the cards stored in a special security sleeve with aluminium foil. As for the ingenuity of the attackers, it is an undeniable fact that they are likely to always be one step ahead. The motivations for finding a vulnerability can differ – money, fame, recognition, or the simple fact that they will achieve something that no one else has achieved before. Well, whatever the attackers’ motivation may be, the impact on the end-customer will be negative, at least from the beginning – loss of money, loss of identity or privacy. I intentionally say that “initially” because the successful exploitation or disclosure of a vulnerability will result in its fixing, there will be one vulnerability less and the world will be more secure – unless two more were created by the patch, of course.
Here is a reminder of basic RFID attacks which can be encountered the most often:
- Reverse Engineering – highly demanding when it comes to the attacker’s knowledge and the knowledge of the protocol itself; the subjects of the RE are the RFID tag or reader themselves.
- Performance analysis - changes in consumption are monitored, when it is possible to distinguish, e.g. whether an incorrect or correct access code was entered
- Eavesdropping & Replay – the attacker uses his reading device to eavesdrop on the communication between the legitimate RFID tag and the terminal/reader. Moreover, in case of a replay attack, he can also repeat some part of the intercepted communication and thus gain sensitive data or accesses in an unauthorized way.
- MitM attack, sniffing – the same as with the eavesdropping on the communication, the attacker inserts himself into the communication between the Tag and the reading device, modifies the captured data and sends this modified data onwards, as if it was the original data.
- Denial of Service – the goal of the attacker is to disrupt the radio signal in order to prevent the communication from happening (e.g. with a jammer).
- Cloning – creating a duplicate/copy of the tag to which the attacker has a physical access
To imagine it better, we list the following real-life situations:
- An attacker can try to get closer to your access card to work with his cloning device while standing in a lunch line or a payment queue.
- A similar risk can be quite real in crowded public transport, where it is possible to get into an unpleasantly close contact with your card.
- Low level of the implemented security vs. motivated attacker can lead to an unlocking of someone else’s hotel room, office, or smart home.
- Underestimating an appropriate RFID tag can allow attackers to manipulate with the balance on travel cards, fitness centre cards, or ski passes.
The impact of many of the attacks described above can be significantly mitigated with encrypted transmission (if supported), filtering techniques, or by selecting a strong authentication method.
We want to explore many of the described attacks in the AEC Hacking Lab and to share the interesting findings with our readers here, in these articles. To understand the topics, it will be necessary to outline the required theoretical background in a simplified format and scope. Today, we will present a very basic division according to the frequency at which the communication is transmitted.
Before we start, it is worth mentioning that when we are talking about the RFID (Radio Frequency Identification) technology, we often come across the abbreviation NFC (Near Field Communication), which is a subset of RFID. The NFC technology enhances and expands the RFID capabilities.
Low Frequency (LF)
Label/abbreviation: LF, frequency: 125 - 134 kHz
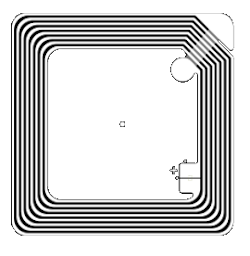
The LF frequency band has a very short, we could say almost touch, reading distance (approx. 20cm) and a low transmission speed. Passive tags are used, which consist of a disk of copper wire and non-rewritable memory. Nowadays, to get a basic reading of an LF tag, it would be sufficient to have one of the newer mobile phones with the Android system. However, it is not entirely true for iOS, where there are a number of "buts" that differ depending on the iPhone model. In most cases, an installation of a third-party application is required for the ability to read the NFC tag, and secondly, the TAG must be specially encoded. If it is not, an iPhone cannot read it. For advanced work with the tag, it is advisable to buy a reader. There are a number of products on the market, differing mainly in functions, supported types and standards.
Examples of use:
- ID cards,
- Identification of components in devices during manufacturing,
- Identification of pets and farm animals,
Manufacturers and their chips:
EM4XX (Unique), HID/ProxCard, Indala, Honeywell, AWID, Nedap NeXS

High Frequency (HF)
Label/abbreviation: HF, frequency: 13.56 MHz
The main difference between the 13.56MHz band and LF lies mainly in the higher reading distance (in case of keeping an active reading distance up to approx. 1 meter). Again, passive tags are mainly used. A lower transfer rate may be a minor disadvantage, and on the contrary, its high reliability in the presence of metals and various fluids is an advantage. The tag antenna is made of copper wire or can be printed with conductive ink on a paper pad and completed with a chip. We distinguish between chips in the RO (Read Only) or RW (Read Write) variant. The capacity ranges from several bytes to kilobytes. Again, for HF tags reding, the same as for the LF tags, we can recommend purchasing a mobile phone with the Android OS (basic information) or one of the readers, for example Proxmark.
Examples of use:
- Attendance and other recording systems,
- Library systems,
- E-wallets, customer loyalty cards,
- Entrance systems.
Manufacturers and their chips:
NXP (MIFARE), HID iClass, Legic, Calypso
Ultra High Frequency (UHF)
Label/abbreviation: UHF, frequency: 860 - 960 MHz
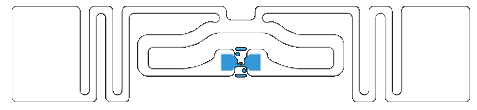
If the information needs to be transmitted over a distance of several meters, then the UHF band is an ideal candidate. Frequency bands vary for UHF systems in different countries. The technology uses the ISO 18000 standard. The UHF technology is used to identify goods and logistics units, allowing the implementation of a unified numerical standard EPC (Electronic Product Code).
Examples of use:
- Identification of goods and logistics units,
- In trucking industry.
Manufacturers and their chips:
RAIN RFID, EPC Gen 2
Microwave frequency band (MW)
Označení/zkratka: MW, frekvence: 2,4 a 5,8 GHz
MW operates close to Wi-Fi networks frequency band. A long reading distance and a high transfer rate are its advantages. The disadvantages include very poor performance in the presence of metal and fluids. The MW frequency band is not working with passive tags, but with active ones, because the tag's own energy source can significantly increase the reading distance, up to tens of meters.
Examples of use:
- Identification of vehicles and moving objects (Real Time Location Services).
Manufacturers and their chips:
Nedap TRANSIT
Conclusion
We outlined the various motivations of attackers and the risks associated with the use of contactless technology. At the same time, we conducted a basic division of RFID technology according to its frequency bands. In the AEC Hacking Lab, we will focus primarily on the LF and HF frequency bands. In order to be able to read RFID tags on the mentioned frequencies and then continue working with them (reading, writing, dumping, cloning), we will need a reading device. In the next article, we will introduce you to Proxmark3, which is an ideal solution for these purposes.



